Most teams rely on cloud platforms to move fast, ship safely, and collaborate from anywhere. That convenience expands your attack surface, so protecting remote and online workloads has to be deliberate.
With clear guardrails, steady monitoring, and disciplined response routines, you can lower risk without slowing product teams.
Know Your Risk Picture
Start with visibility. Map your business-critical workloads, the data they access, and the internet-exposed entry points. Inventory third-party identities, ephemeral environments, and shadow resources spun up for experiments.
Turn findings into a short backlog so the riskiest gaps are closed first. An ENISA threat review documented thousands of significant incidents across 2024 and 2025, underscoring how fast tactics evolve and why fresh intelligence should shape your roadmap.
Identity, Access, And Segmentation
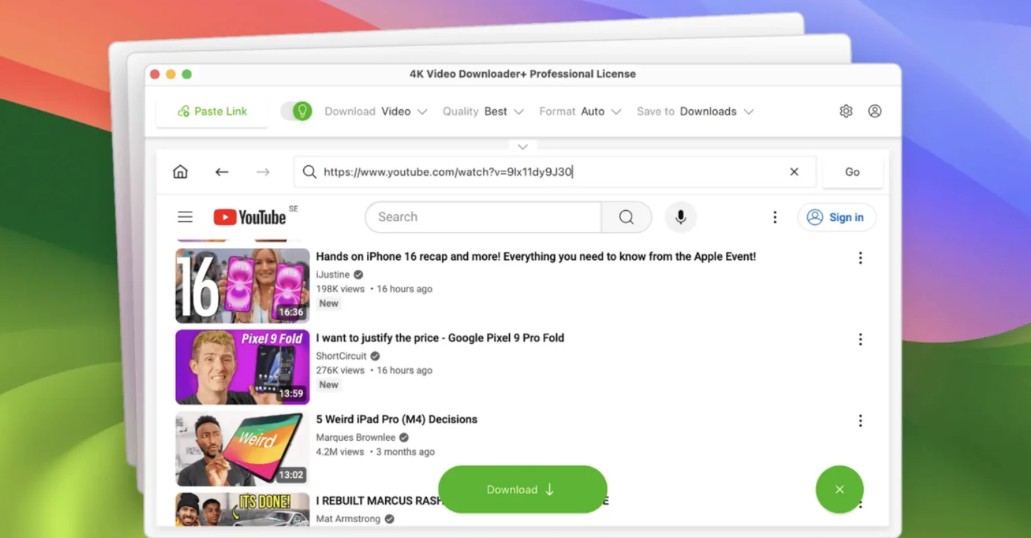
Identity is the new perimeter. Standardize roles, scopes, and naming conventions so that dangerous grants are easy to identify, and consult Cloud Security monitoring and management tips to make those patterns easier to replicate. Segregate production from development and split sensitive workloads into smaller trust zones that limit lateral movement.
Use just-in-time elevation with approvals for break-glass work. Rotate secrets and keys on a schedule and on role changes, and revoke third-party OAuth grants the same day they are no longer needed.
Treat identity catalogs as living documents that evolve as your architecture grows. Consistent reviews help uncover stale accounts, unused permissions, and overbroad access paths that quietly increase risk.
Network micro-segmentation reinforces these efforts by ensuring that even valid identities cannot reach systems they do not need. Automated access workflows further reduce human error by enforcing standardized approval paths.
Shift To A Zero Trust Mindset
Legacy castle and moat thinking does not fit modern architecture. Assume the network is untrusted, verify each request, and grant only the least privilege required.
Add device health checks for admin tasks, require phishing-resistant MFA, and use short-lived tokens so access expires quickly. CISA guidance frames it bluntly: act as if an attacker is present, enforce per-request decisions, and log every allow and deny so you can explain them later.
This shift means mapping every workflow to understand who needs what and when. You reduce implicit trust by breaking large permissions into smaller, purpose-built roles that limit blast radius.
Continuous validation becomes a habit, not a one-time setup, which helps teams catch misconfigurations early. Automated policy engines further reinforce consistency by applying the same checks across all environments.
Data Protection That Travels With The Workload
Encrypt data in transit and at rest everywhere, with managed keys and strict separation of duties. Prefer private service endpoints to public exposure, then restrict egress so workloads cannot talk where they do not need to.
Backups should be immutable, isolated, and tested with application-level checks. Keep scanners in pipelines to block public buckets, weak TLS, and overly broad service roles before they ship.
- Classify data and tag it so tools can enforce policy.
- Enforce least privilege and short sessions for humans and services.
- Require strong MFA for admins and service owners
- Segment networks by sensitivity with tight egress rules
- Centralize secrets and auto-rotate them on a cadence.
- Test restores monthly andrecordsd real recovery times
Continuous Detection And Rapid Response
Monitoring should focus on what matters most. Baseline normal behavior for privileged identities and critical data stores, then alert on deviations instead of drowning teams in noise.
Route high-priority alerts to on-call rotations with first steps automated, like isolating a role or pausing a pipeline. Run quarterly table-top exercises that include engineering, legal, and customer teams.
IBM’s breach cost research found that organizations cut losses by shortening detection and containment windows, reinforcing the value of faster triage, decisive isolation, and rehearsed recovery steps.
Cloud Security Monitoring Playbook
Keep a small set of dashboards for auth anomalies, network egress spikes, data access outliers, and control plane changes.
For each signal, define an owner, an SLA, and a first action. Add suppression rules for noisy patterns and enrich alerts with runbook links so responders move faster. Trim any alert that never changes behavior.

Proving Security With Evidence
Security earns trust when you can show it works. Document policies inside the tools people already use, not in forgotten wikis. Publish monthly notes on fixes shipped, drills run, and mean time to contain for sensitive workloads.
Align your roadmaps to threat intelligence summaries so stakeholders see why priorities shift. Finally, review incidents openly, capture the top three lessons, and bake improvements into templates so every team benefits.
Remote and online workloads will keep expanding with the business. Make protection a set of small, reliable habits that evolve with the threat vista.
When visibility, least privilege, and fast response become the default, risk falls, and delivery stays quick. Track results, improve a little each sprint, and your program will stay effective without becoming a drag on momentum.